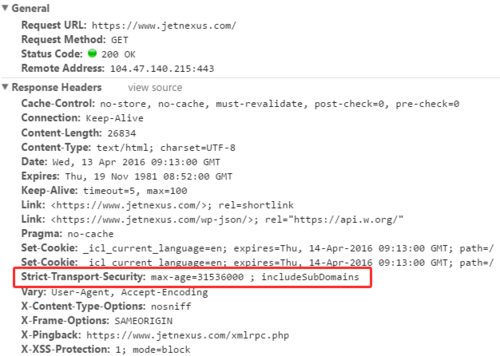
It’s amazing that so many specific and active steps still need to be taken to ensure our clients’ and their HTTPS traffic really are as secure as we and they hope. Luckily those steps are quick and simple when you can utilise our flightPATH traffic management rules. flightPATH is a dynamic, event-based rule engine developed by edgeNEXUS to intelligently manipulate and route load balanced IP, HTTP and HTTPS traffic. It is highly configurable and powerful, yet very easy to use. One of those rules allows you to add a Strict-Transport-Security HTTP header to web server responses served through sites protected by SSL/TLS.
The Strict-Transport-Security HTTP header and value ensure that your site’s clients will only ever make requests over https://. Even if your real web servers are sitting behind a proxy or load balancer (you know, a edgeNEXUS ALB-X) and are unaware their content is actually served over https://, if they send https:// links in responses, the client will still use https:// for any links. In other words, whether our real web servers are sending secure links or not, clients will ensure any links they follow are.
If your developers make a mistake, or the operations team do; no problem. There’s no chance a client browser will make an insecure request as long as they receive and act upon this header (which all popular contemporary browsers do). Assuming a client arrives at your actual SSL/TLS protected site, you can help ensure they will do so securely and consistently thereafter. We’ve a rule for redirecting HTTP requests to HTTPS too, just in case you need that (you’ll find it installed by default).
This is one of many flightPATH traffic management rules you can deploy to improve the security of your site and it’s users. For others that are just as easily deployed in a few clicks see our blog.
As we often point out, the great benefit of using a load balancer is that we only have to do this in a single place in order to deploy this to all our servers (and sites). We don’t need to rely on developers or Apache re-configurations. On the edgeNEXUS load balancer we just import a jetPACK configuration template and assign a flightPATH traffic rule to whichever Virtual Service(s) we wish to protect.
The rule only adds the header if it doesn’t exist so it’ll work even where our web servers already insert it or perhaps only insert it for specific pages. This rule should be part of your standard Virtual Service configuration – you’ve nothing to lose whatever the site, although of course, testing is always recommended. You can download this jetPACK and many others on the edgeNEXUS Github site here
This is one of many flightPATH rules we’ve developed, which you can deploy to improve the security of your site and it’s users. For more around security related HTTP Headers, check out these articles:
- Simplifying Security HTTP Headers with edgeNEXUS Traffic Management: X-Content-Type-Options
- A HTTP Security Header to Combat ‘Clickjacking’ – How to Improve your Site’s Security with the X-Frame Options Header